Question 1:
Which of the following host addresses are members of networks that can be routed across the public Internet?(Choose three.)
A. 10.172.13.65
B. 172.16.223.125
C. 172.64.12.29
D. 192.168.23.252
E. 198.234.12.95
F. 212.193.48.254
Answer: CEF
Explanation:
Private IP address scheme
Class A: 10.0.0.0 – 10.255.255.255
Class B: 172.16.0.0 – 172.31.255.255
Class C: 192.168.0.0 – 192.168.255.255
Other then private ip addresses remaining IP’s addresses are routed across internet.
Question 2:
Given a subnet mask of 255.255.255.224, which of the following addresses can be assigned to network hosts?
(Choose three.)
A. 15.234.118.63
B. 92.11.178.93
C. 134.178.18.56
D. 192.168.16.87
E. 201.45.116.159
F. 217.63.12.192
Answer: BCD
Explanation:
For calculating network hosts range for subnet 255.255.255.224
Simple method to find out network subnet is 256 -224 = 32
Write down the multiples of 32 to get subnet networks
Host range for subnet 255.255.255.224 are between this ranges below
0 ----- 31 (0 is network address and 31 is broadcast address)
32 -----63
64 -----95
96 -----127
128 ----159
160---- 191
192 ----223
224 ----255
Question 3:
When variable length subnet masking is used, what does the term route aggregation describe?
A. calculating the total number of available host addresses in the AS
B. combining routes to multiple networks into one supernet
C. reducing the number of unusable addresses by creating many subnets from one supernet
D. reclaiming unused address space by changing the subnet size
Answer: B
Explanation:
Route aggregration is an effort to route smaller prefixes via an aggregated larger prefix (supernetting). The advantage is obvious: Many /24 networks, for example, could be aggregated to larger networks like /23, /22 or even bigger prefixes.
Question 4:
ABC Company is merging with several local businesses that use routers from multiple vendors. Which routing protocol would work best to connect ABC Company with the enterprise networks it has acquired by providing scalability and VLSM support while minimizing network overhead?
A. RIP v1
B. RIP v2
C. IGRP
D. OSPF
E. EIGRP
Answer: D
Explanation:
Since only OSPF,EIGRP and RIPv2 supports VLSM in above options. It requires working with multi vendor and providing scalability OSPF is best choice of the three mentioned.
Question 5:
Which of the following IP addresses fall into the CIDR block of 115.64.4.0/22? (Choose three.)
A. 115.64.8.32
B. 115.64.7.64
C. 115.64.6.255
D. 115.64.3.255
E. 115.64.5.128
F. 115.64.12.128
Answer: BCE
Explanation:
/22 is 8bits + 8bits + 6bits i.e 11111111.11111111.11111100.0
Third octet 11111100 = 128+64+32+16+8+4
= 252 therefore subnet mask is 255.255.252.0
Subnet networks are 256-252= 4
Host range for above subnet are
0------- 3
4 ------ 7
Host that fall under 115.64.4.0 /22 networks are
4 5 6 7
Question 6:
In the implementation of VLSM techniques on a network using a single Class C IP address, which subnet mask is the most efficient for point-to-point serial links?
A. 255.255.255.0
B. 255.255.255.240
C. 255.255.255.248
D. 255.255.255.252
E. 255.255.255.254
Answer: D
Explanation:
For point-to-point serial link exist only two hosts so the best possible subnet mask for two useable hosts for class C network is 255.255.255.252
Question 7:
Which statements are true regarding classless routing protocols? (Choose two.)
A. The use of discontiguous subnets is not allowed.
B. The use of variable length subnet masks is permitted.
C. RIP v1 is a classless routing protocol.
D. IGRP supports classless routing within the same autonomous system.
E. RIP v2 supports classless routing.
Answer: BE
Question 8:
The company internetwork is subnetted using 29 bits. Which wildcard mask should be used to configure an extended access list to permit or deny access to an entire subnetwork?
A. 255.255.255.224
B. 255.255.255.248
C. 0.0.0.224
D. 0.0.0.8
E. 0.0.0.7
F. 0.0.0.3
Answer: E
Explanation:
29 bits subnet is 8bits + 8bits + 8bits + 5bits
255.255.255.(5bits)
11111000 = 128+64+32+16+8+0+0+0
= 248
Subnet is 255.255.255.248
Simple method to calculate the Wildcard mask from known subnet is to
Reverse 1’s into 0’s and 0’s into 1’s from the binary representation of subnet.
For above example (248 = 11111000 subnet)
11111000 (subnet) = 00000111 (wildcard mask) last octet.
= 7 (wildcard mask) for last octet.
Converting the remaining first 3 octets of subnet into wildcard mask using above method
Resulted wildcard mask is 0.0.0.7
The MDA Company is implementing dialup services to enable remote office employees to connect to the local network. The company uses several different Layer 3 protocols on the network. Authentication of the users connecting to the network is required for security. Additionally, some employees will be dialing long distance and will need callback support. Which protocol is the best choice for these remote access services?
A. 802.1
B. Frame relay
C. HDLC
D. PPP
E. SLIP
F. PAP
Answer: D
Question 10:
Refer to the diagram. All hosts have connectivity with one another. Which statements describe the addressing scheme that is in use in the network? (Choose three.)
 A. The subnet mask in use is 255.255.255.192.
A. The subnet mask in use is 255.255.255.192.B. The subnet mask in use is 255.255.255.128.
C. The IP address 172.16.1.25 can be assigned to hosts in VLAN1
D. The IP address 172.16.1.205 can be assigned to hosts in VLAN1
E. The LAN interface of the router is configured with one IP address.
F. The LAN interface of the router is configured with multiple IP addresses.
Answer: BCF
Question 11:
Which routing protocols will support the following IP addressing scheme? (Choose three.)
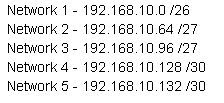 A. RIP version 1
A. RIP version 1B. RIP version 2
C. IGRP
D. EIGRP
E. OSPF
Answer: BDE
Question 12:
A company with 25 computers decides to connect its network to the Internet. The company would like for all of the computers to have access to the Internet at the same time, but the company only has four usable public IP addresses. What should be configured on the router so that all computers can connect to the Internet simultaneously?
A. static NAT
B. global NAT
C. dynamic NAT
D. static NAT with ACL’s
E. dynamic NAT with overload
Answer: E
Question 13:
A network administrator would like to implement NAT in the network shown in the graphic to allow inside hosts to use a private addressing scheme. Where should NAT be configured?
 A. Corporate router
A. Corporate routerB. Engineering router
C. Sales router
D. all routers
E. all routers and switches
Answer: A
Question 14:
Which of the following describe private IP addresses? (Choose two.)
A. addresses chosen by a company to communicate with the Internet
B. addresses that cannot be routed through the public Internet
C. addresses that can be routed through the public Internet
D. a scheme to conserve public addresses
E. addresses licensed to enterprises or ISPs by an Internet registry organization
Answer: BD
Question 15:
Refer to the graphic. A host is connected to switch port Fa0/3 with a crossover cable. The host and switch have been fully configured for IP connectivity as shown. However, the port indicator on switch port Fa0/3 is not on, and the host can not communicate with any other hosts including those connected to VLAN 2 on the same switch. Based on the information given, what is the problem?
B. The cable is the wrong type.
C. The switch has been assigned an incorrect subnet mask.
D. Switch port Fa0/3 has been blocked by STP.
E. The switch and the hosts must be in the same subnet.
Answer: B
Explanation:
Straight through cable is used to connect a host to switch.
Question 16:
What kind of cable should be used to establish a trunked link between two Catalyst 2950 switches?
A. a straight-through cable
B. an EIA/TIA-232 serial cable
C. an auxiliary cable
D. a modem cable
E. a cross-over cable
Answer: E
Explanation:
Cross-over cable is used to connect two switches.
Question 17:
What is the purpose of Spanning Tree Protocol?
A. to prevent routing loops
B. to create a default route
C. to provide multiple gateways for hosts
D. to maintain a loop-free Layer 2 network topology
E. to enhance the functions of SNMP
Answer: D
Question 18:
The network 172.25.0.0 has been divided into eight equal subnets. Which of the following IP addresses can be assigned to hosts in the third subnet if the ip subnet-zero command is configured on the router? (Choose three.)
A. 172.25.78.243
B. 172.25.98.16
C. 172.25.72.0
D. 172.25.94.255
E. 172.25.96.17
F. 172.25.100.16
Answer: ACD
Question 19:
Which wild card mask will enable a network administrator to permit access to the Internet for only hosts that are assigned an address in the range of 192.168.8.0 through 192.168.15.255?
A. 0.0.0.0
B. 0.0.0.255
C. 0.0.255.255
D. 0.0.7.255
E. 0.0.3.255
Answer: D
Question 20:
The exhibit shows a company network. The network administrator would like to permit only hosts on the 172.30.16.0/24 network to access the Internet. Which wild card mask and address combination will only match addresses on this network? 
B. 172.30.16.0 0.0.0.255
C. 172.30.0.0 0.0.15.255
D. 172.30.16.0 0.0.31.255
E. 172.30.16.0 0.0.255.255
Answer: B

40 comments:
Question 12
I hope you meant answer E to refer to Port Address Translation or Overloading NAT.
HI,
Yes its Dynamic NAT with overload.
Updated the E option for Question 12.
Cheers
what is the ip subnet zero command. i dont get it still.at 18. question ?
Hi,
ip subnet-zero global configuration command was required to be able to configure subnet zero on an interface. In Cisco IOS 12.0, ip subnet-zero is enabled by default.
example:
10.0.0.0 /10
subnet mask: 255.192.0.0
the different subents for the above network are
10.0.0.0
10.64.0.0
10.128.0.0
10.192.0.0
Out of these four subnets, FIRST subnet(10.0.0.0) is called subnet zero and the LAST subnet(10.192.0.0) is called all-ones subnet, respectively.
To use this 10.0.0.0 network on interface you need to enable ip subnet zero command on global config mode.
Hope this helps
Cheers!!!
I am still very confused about question 18. I don't understand how to get those numbers.
You're borrowing eight bits from the host portion of the subnet mask, because you're wanting eight subnets. The default subnet is 255.255.0.0. Eight bits would bring the subnet mask to 255.255.255.0. I am just very confused here. Help!
Hi Darla,
Q18 tells network 172.25.0.0 has divided into 8 equal subnets
i.e
to get 8 equal subnets we need to borrow 3 bits for subnet from host bits in 3rd octet.
8bits + 8bits + 1110 0000
subnet is 255.255.224.0
usable host range with ip subnet zero enable for all 8 subnets
subnet 0 host range :
172.25.0.1 - 172.25.31.254
subnet 1 host range :
172.25.32.1- 172.25.63.254
subnet 2 host range :
172.25.64.1 - 172.25.95.254
subnet 3 host range :
172.25.96.1 - 172.25.127.254
subnet 4 host range :
172.25.128.1 - 172.25.159.254
subnet 5 host range :
172.25.160.1 - 172.25.191.254
subnet 6 host range :
172.25.192.1 - 172.25.223.254
subnet 7 host range :
172.25.224.1 - 172.25.255.254
the question is asking for selecting the hosts for third subnet from the above 8 subnets i.e subnet 2(third subnet) host ranges.
Hope this helps
Cheers!!!!
Thank you so much! I see where my mistake was.
You've helped a lot. =)
Question#5,
Why you pick "7" as part of the choice? I thought 7 is a broadcast address.
Please explain.
q5 asks addresses fall into the CIDR block of 115.64.4.0/22
4 - 7 is the subnet range
115.64.4.0 (ntw addr) - 115.64.4.255 (broadcast addr).
115.64.5.0 (ntw addr) - 115.64.5.255 (broadcast addr).
115.64.6.0 (ntw addr) - 115.64.6.255 (broadcast addr).
115.64.7.0 (ntw addr) - 115.64.7.255 (broadcast addr).
Since the option B IP 115.64.7.64
is valid host.
Important its CIDR or VLSM enable so we can use the 1st (4) and last (7) subnet networks.
Hope this helps
Cheers
Question 10
Shouldn't the IP address of Host A on VLAN 1 be 172.16.1.26 rather than 172.16.1.126 which is an overlapping address of Vlan 2 using a mask of 255.255.255.128
Q10:
Subnet mask is 255.255.255.128
different subnetworks are
172.16.1.1 - 172.16.1.127 (valid host range 1 to 126 VLAN1)
172.16.1.128 - 172.16.1.255
Therefore the IP address 172.16.1.126 is not overlapping with 172.16.1.129 (VLAN2) address
Hope this helps
CHEERS!!!!
This blog is jst great...
Q19
sir, cud u elaborate further how u ended up with Ans. D
Thank u so much.
Hi
Q19
host range of 192.168.8.0 through 192.168.15.255 only needed to permit.
For the above range subnet mask is
255.255.248.0
Simple method to calculate the Wildcard mask from known subnet is to
Reverse 1’s into 0’s and 0’s into 1’s from the binary representation of subnet mask.
For above example (248 = 11111000 subnet)
11111000 (subnet) = 00000111 (wildcard mask) third octet.
= 7 (wildcard mask) for third octet.
Converting the remaining first 2 and last octets of subnet into wildcard mask using above method
Resulted wildcard mask is 0.0.7.255
Hope this helps
cheers!!!
thank u so much for d reply...
now getting the wilcard mask is quite handy...but how wer u able to get the subnet mask for d given range of ips >> 192.168.8.0 to 192.168.15.255?
sorry...a newbie here :(
Hi,
In Q19 to get the subnet mask for given range on IP address
192.168.8.0 to 192.168.15.255.
Total number hosts in the above ip range is 2046.
to get this above number we need to have 11 bits for host part and remaining 21 (32-11=21bits) bits for subnet .
2 power 11 is 2048
to get valid hosts it supports 2 power 11 - 2 = 2046
subnet mask for 21 bits is
8bits + 8bits + 11111000 + 00000000
= 255.255.248.0
Hope this helps
Cheers
Hi.
Q10
How do you know that the subnet mask is 255.255.255.128, and not 255.255.255.192?
Please explain to me.
Thank you.
Hi
Q10,
The exhibit provides VLAN 1 is with 84 hosts, with Host A IP address 172.16.1.126
To get a subnet mask for 84 hosts we need to borrow 7 bits for host portion.
2 power 7 - 2
= 128-2 = 126 valid hosts
Subnet mask is 255.255.255.128
different subnetworks are
172.16.1.1 - 172.16.1.127 (valid host range 1 to 126 VLAN1)
172.16.1.128 - 172.16.1.255
Whereas 255.255.255.192 can only provide 64 hosts per subnet we need 84 hosts (VLAN1) and 114 hosts (VLAN2) as per the exhibit in Question.
Hope this helps
CHEERS!!!!
This website is very useful. Thanks a lot.
Q6 - The asnwer of ...252 is not correct. You can use a 254 mask on serial links using the 'no ip directed-broadcast' command. The Lower host address also serves at the net address and there is no broadcast needed because it is a point to poin link.
Q6 only concern is VLSM techniques on a network using a single Class C IP address, which subnet mask is the most efficient for point-to-point serial links.
Yes your correct but your option needs additional commands to achieve it.
Thats why we need to go for .252 as per question requirement.
Hope this helps
Cheers
Hi,
Q20 if access list is created, where should be placed?Also this access list should be extended or standart?
I'll apreciate your answer.
Cheers,
Do
Hi Do,
We need to create Extended ACL because we need to permit Web traffic (port based)
As per the exhibit We need to place the ACL on R1 interface which is connecting to another router towards Internet.
The direction of ACL will be OUT.
Ps: Extended ACL needs to be placed near to source But since the other network(172.30.18.0) traffic will be permited to internet for this reason we have to choose other interface near to the internet on R1 with OUT direction so that only 172.30.16.0 network will be permited to internet.
Hope this helps
Cheeers
Hi,
Can you pls explain question 9?
Tks
Hi Leonardo,
Q9:
Explanation:
Considerations to be taken to select the WAN protocol based on the question requirements are
1. Multiple layer 3 protocols used.
PPP supports multiple layer3 protocols
2. Authentication required to users .
PPP provides this by using CHAP / PAP authentication method
3. callback support
Callback is one of the features that PPP support.
Since all requirements of the company is fullfilled by PPP we have selected option D
Hope this helps
Cheers
Q4 answer should be EIGRP, since it supports VLSM also it is not proprietary Cisco which means multiple vendor network devices can be used…?
hi
Question 4.
EIGRP is a CISCO proprietary routing protocol.
Please verify it at cisco.com
OSPF is the correct option.
Hope this helps
Cheers
You are right OSPF is the correct answer since EIGRP is Cisco Prop..
Thanks
Hi!!!
butt.... how do you know the number of host?
--------
Hi,
In Q19 to get the subnet mask for given range on IP address
192.168.8.0 to 192.168.15.255.
Total number hosts in the above ip range is 2046.
Hi - Thanks for this awesome blog.
I just have a question in regards to Question# 4. Why we do not select Answer# B (RIP v2). The question states that we have to take the network overhead in consideration.
What are your thoughts?
Hi Remon,
The question 4 also has providing scalability and minimizing network overhead
Scalability is acheived by using OSPF and OSPF only has overhead only during intial convergence state but later it has less network overhead compared to regular interval updates by RIP v2
Hope this helps
Cheers
hi a3tips,
1st: thanks for this awesome blog! it helps a lot !!!
on q5: I do understand your explanation 90% the only thing I dont know is: how do you know the range is 0-4 and 5-7. I mean, the increment is 4, I understand, but from what can I determine to "stop" incrementing with 4? Why is it not 8-12 and so on?
many many thanks, //sepp
Hi,
Q5:
Host range for above subnet are
0------- 3
4 ------ 7
and so on..
Why i stoped at 7 is since Q5 address 115.64.4.0/22? falls here..
Hope this helps
Cheers
oops, thats a bit embarassing... thx a3tips.
I have one additional question which is really important for me: I am very confused about the following: will the TAB key work on the exam? I am using tab-key all the day in my normal work and I really dont know all commands by heart. I was reading a lot of different statements regarding that, but I evaluate your blog as most relieable and would be keen on your statement.
many thanks in advance,
//sepp
Hi,
The help command ( ? ) works in test. which shows all the available commands
This will help you to fill entire command statement
Hope this helps
Cheers
Hi a3tips...
Thanks for this blog...
In q19... is it really possible to use 192.168.0.0 /21 ?
I'm confused since 192.168.0.0 is a class C address. So it will be like:
Net.Net.Net.Host
and can only have 256 maximum host in a subnet.
Hi,
Q19:
Yes as far as Class C hosts consist of 254 hosts
If we use VLSM / CIDR (Subnetting an subnet ) which allows us to borrow subnet bits to host portion ..
So for your question yes it allows /21 bit for Class C address
HTH
Cheers!!!
Q.18
D is a broadcast address. That cant be assigned to a host. Is this a typo. (172.25.94.255)
Yes Q18 answer D is a typo mistake..
Cheers
Awesome!
Im due to take the exam soon. Learning alot from this site and several others. Thanks alot.
Post a Comment